Tag Archive for: security
The Top Ten IoT Vulnerabilities
Managed Network Services, Security
Kevin Ashton coined the phrase the “Internet of Things” (also known as “IoT”) back in 1999. This term represented the concept of a massive system where everyday appliances would communicate with each other through omnipresent sensors.
Since…

The Week in Breach
Managed Network Services, Security
Breach news to share
with your customers!
This week, ransomware shuts
down a food bank, Canadian patient data is leaked via employee email, and
Australian universities…

“You can’t relax”: Here’s why 2-factor authentication may be hackable
Managed Network Services, Security
PUBLISHED SAT, JAN 5 2019 11:09 AM ESTUPDATED SAT, JAN 5 2019 1:20 PM ESTJennifer Schlesinger@JENNYANNE211Andrea Day@ANDREADAY
KEY POINTS
Cybercriminals can now use a type of phishing to get around two-factor…

Week in Breach
Security
The Week in Breach: 05/28/19 - 06/04/19
By Kevin Lancaster on Jun 5, 2019 3:59:56 PM
This week, malware infects POS systems of US fast-food chain, ransomware continues to impact local governments, and a phishing scam tricks…

3 Tips to Secure Password Management
Security
JL Peck CISMLead Consultant Treat your password like your toothbrush. Don't let anybody else use it, and get a new one every six months.— Clifford Stoll
One of the common areas we see companies and technology groups struggling to manage…

Week in Breach
Security
This
week, hackers continue to phish for patient data from US healthcare providers,
a British police website goes down, and Australians see a spike in credential
stuffing attacks.
Dark Web ID Trends:
Top Source
Hits: ID Theft Forum…
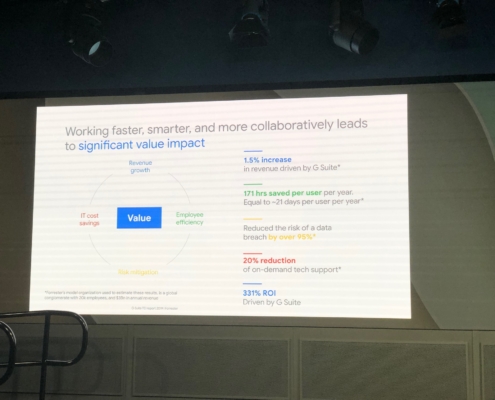
The Value of the G-Suite.
Innovative Ideas, Managed Network Services, Productivity, Security
Yesterday my CIO and I got a chance to visit the Google campus to listen and experience how AI is already increasing productivity, security, and reducing the burden on IT, to drive increase revenue for clients who view technology as a strategic…

Week in Breach
SecurityThis week, US students hack into school, Canadian alcohol gets held for ransom(ware), New Zealand outdoors retailer is exposed, and data doesn’t expire on the Dark Web.
Dark Web ID Trends:
Top Source Hits: ID Theft Forums (99%)
Top…

Four key security tips when using any collaboration technology
Managed Network Services, Security
Gerald Beuchelt, CISO, LogMeInMarch 19, 2019
With database breaches and ransomware attacks making daily news, security is now a top priority for companies, and collaboration solutions are no exception. In the current age…

6 Tips to Help Your Startup Optimize Workflow
Innovative Ideas, Managed Network Services, Managed Print Services, Productivity, Security
Startupgrind
MARGARITA HAKOBYAN | A YEAR AGO
One of the biggest challenges for a startup is to accomplish its lofty goals with limited resources. Finding a way to get from Point A to Point B without crashing and burning can be…
